insomnia-plugin-sfsf-samlassertion
This is an Insomnia plugin for generating SAML Assertions required to obtain OAuth tokens from SAP SuccessFactors API's, as described in the SAP SuccessFactors HXM Suite OData API: Developer Guide (V2) documentation Generating a SAML Assertion and the blog SAML assertions for SAP SuccessFactors OAuth 2.0 API’s: Handling of User Identifiers. Based on the npm package saml from auth0.
SAP Community Blog with more details about the plugin usage: https://blogs.sap.com/2023/02/02/testing-successfactors-apis-how-to-use-insomnia-to-automate-the-generation-of-saml-assertions/
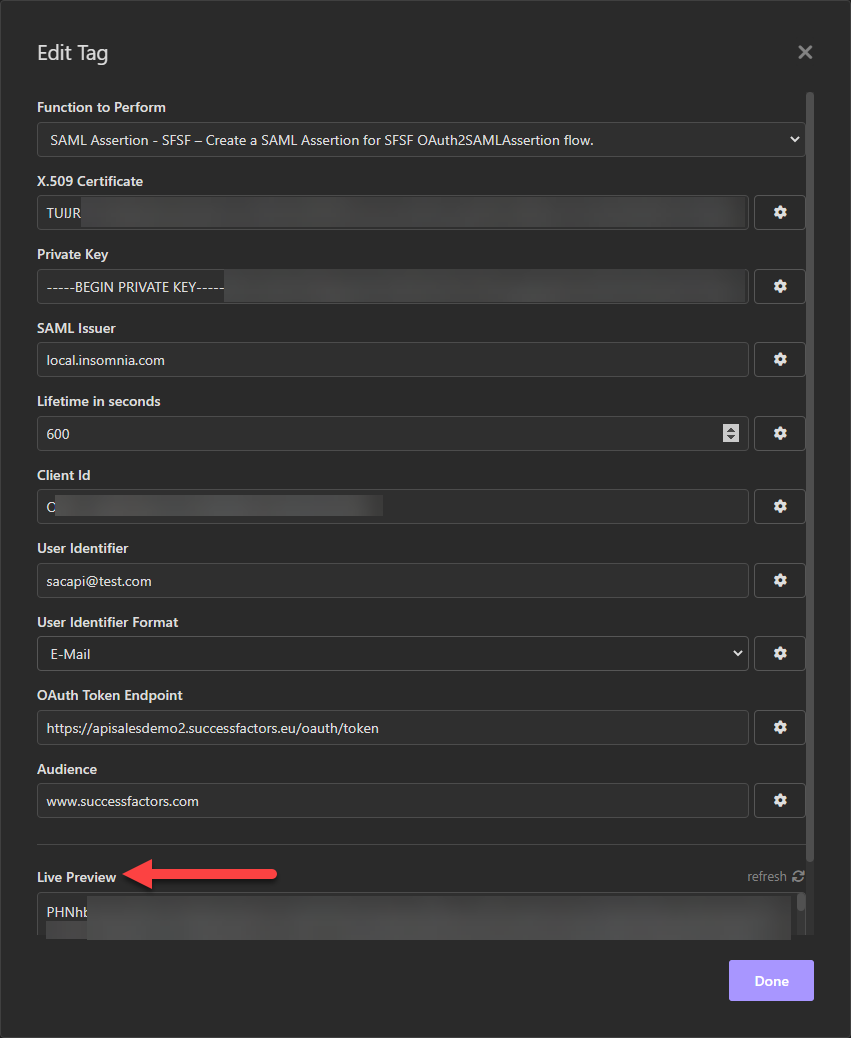
After successfully installing the plugin, the Template Tag SAML Assertion - SFSF will be available and the following parameters have to be entered to generate a SAML Assertion:
- X.509 Certificate: Public certificate corresponding to the key pair used for client configuration in SAP SuccessFactors.
- Private Key: Private key of the key pair that will be used to sign the SAML assertion.
- SAML Issuer: Name of the IdP issuing the SAML Assertion. The proposed value local.insomnia.com should be a good starting point.
- Lifetime in seconds: Lifetime of the SAML Assertion in seconds.
- Client Id: Registered Client Id in SAP SuccessFactors, also called as API key in the SFSF Documentation.
- User Identifier (Changed on April/2023): User identifier to be used to access the SAP SuccessFactors API's.
- User Identifier Format (Added on April/2023): Type of User Identifier informed for SAML assertion. It can be one of the three following types: User ID, Username or E-Mail. Check the blog SAML assertions for SAP SuccessFactors OAuth 2.0 API’s: Handling of User Identifiers to better understand which of these options best suits your test needs.
- OAuth Token Endpoint: The URL of the API server from which you request the OAuth token.
- Audience: Value used to tag the SAML assertion. The proposed value www.successfactors.com should be a good starting point.
- Delay (Seconds): Delays the handover of the SAML assertion to Insomnia runtime. Useful when errors like "The SAML assertion has expired" are observed, but actually the request is reaching the endpoint before the validNotBefore date from SAML assertion.
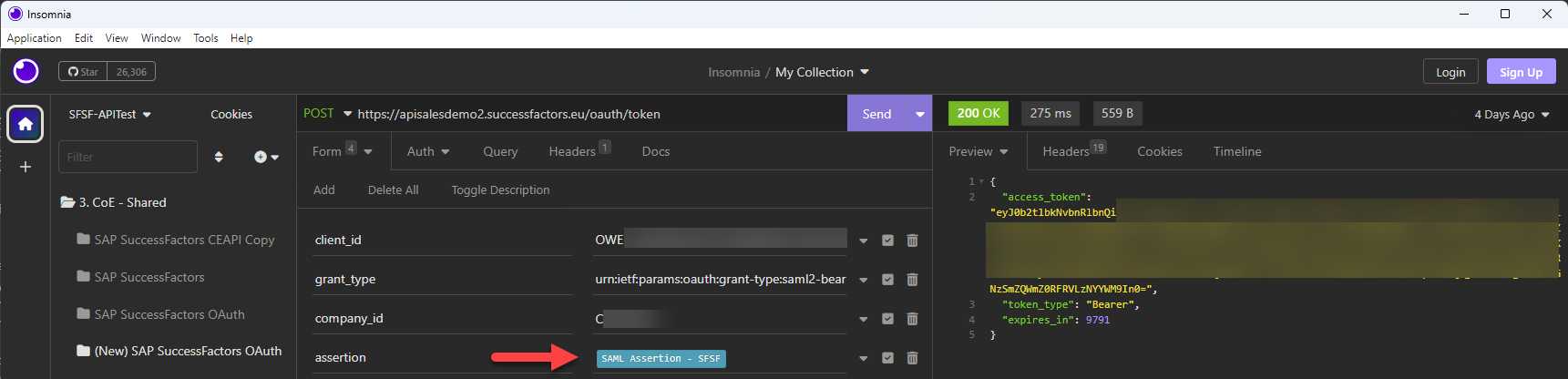
Add the Template Tag and configure it where the SAML assertion is required. The SAML Assertion will be generated and returned in the Base64 format.