Get more details on encrypt-attr
npm i directus-extension-encrypt-attr
Find and copy folder "directus-extension-encrypt-attr" from "/node_modules" to "/extensions"
File: .env
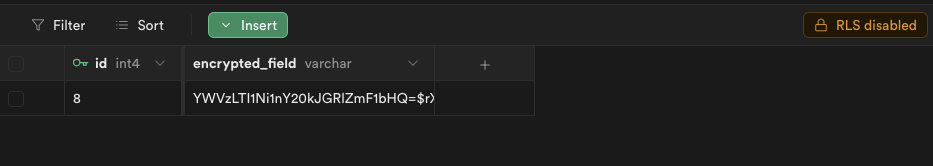
EA_KEYS={"default": "32Bytes_long_cryptographically_random_key"}
EA_KEY_ID="default"
| NAME | Required | Default value |
|---|---|---|
| EA_KEYS | YES | |
| EA_KEY_ID | NO | default |
| EA_VERIFY_ID | NO |
All keys should be 32 bytes long, and cryptographically random. Manage these keys as you would any other sensitive credentials (environment config, vault, keychain). You can generate random keys with this snippet:
This is designed to protect you from leaking sensitive user data under very specific scenarios:
- Full data dump
- Misplaced unencrypted backups
- Compromised database host
- Partial data dump
- Query injection via unsanitized input
Specifically, this does not provide any protection in cases of a compromised app host, app-level vulnerabilities, or accidentally leaking sensitive data into logs. It is also not a substitute for actually encrypting your backups, sanitizing your input, et cetera.
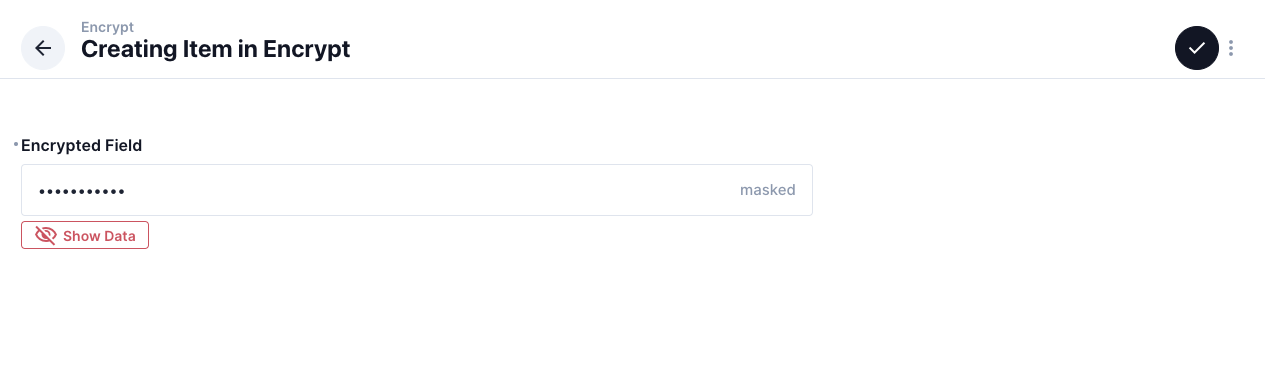
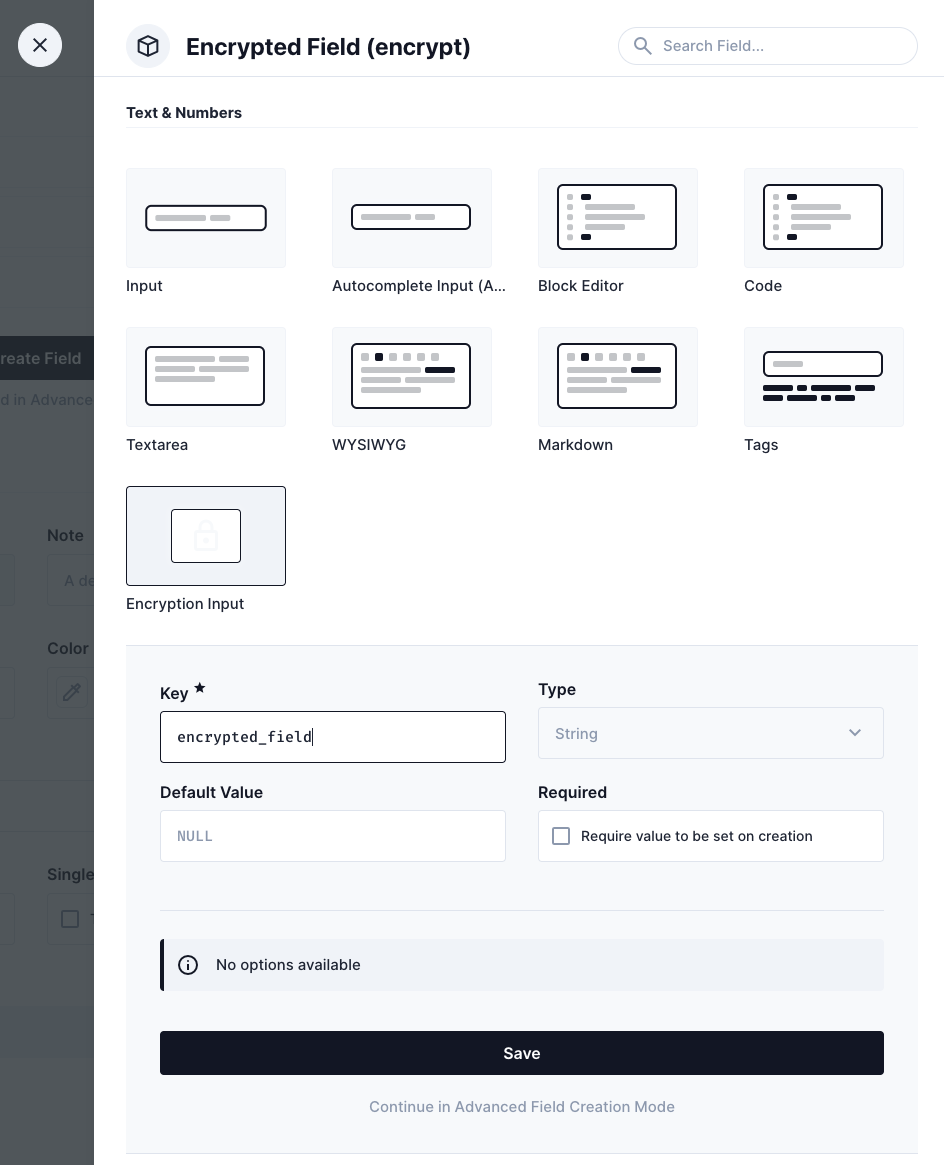
Add a new field with "Encryption Input"
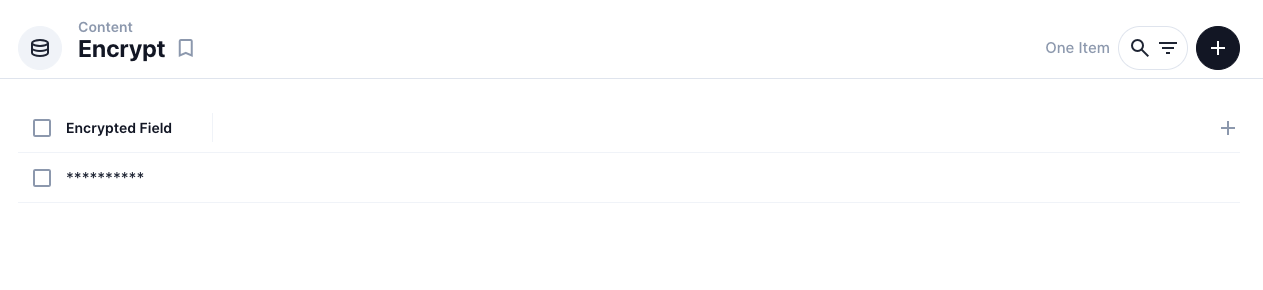
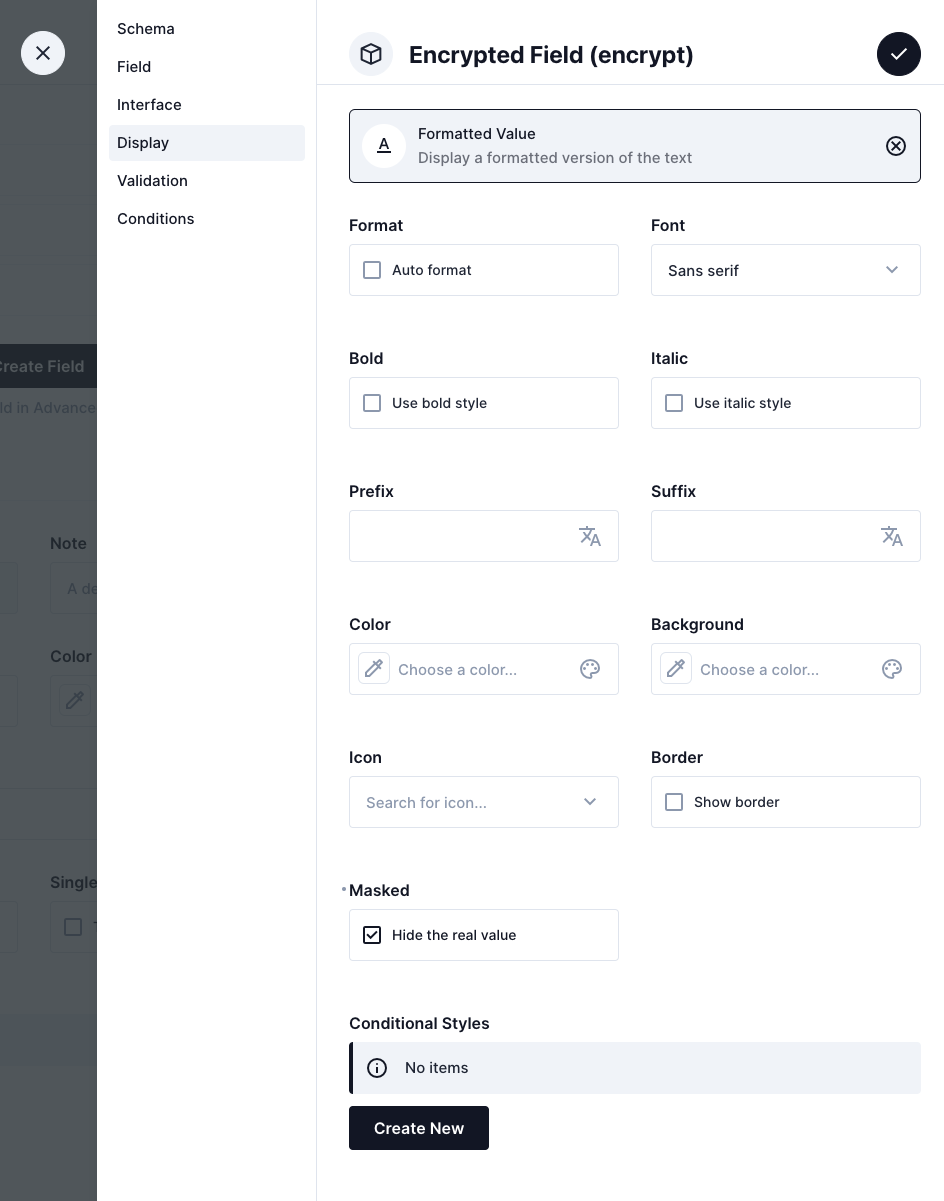
To hide the real value in item list In "Display", choose "Formatted Value", then Check "Masked"
https://github.com/Drunkenpilot/directus-extension-encrypt-attr/issues
BSD-3-Clause